Maintaining privacy can be a challenge in an era where digital footprints are becoming increasingly traceable. There may be instances where you need to send an anonymous email. That means posting digital mail without revealing your identity.
This could be for many reasons, such as whistleblowing, sending a secret admirer note, or simply maintaining your privacy online. Whatever your reasons, this comprehensive guide will walk you through the process of sending an anonymous email.
Why Anonymous Email is Important
Before diving into the process, it's crucial to understand why you might want to send an anonymous email. Anonymity can be a protective shield, ensuring your personal information remains confidential.
It's a way to communicate without fear of reprisal or judgment. However, it's essential to remember that using anonymity for illegal activities is against the law and can lead to severe consequences. Anonymity should be used responsibly, with respect for other's privacy, and within legal boundaries.
Here's how you can send an anonymous email;
Step 1. Choose an Anonymous Email Service
There are several anonymous email services available that allow you to send emails without revealing your identity. These services do not require personal information to create an account and use end-to-end encryption to protect your privacy.
Each service has unique features, so it's worth researching to find the one that best suits your needs. Some popular options include:
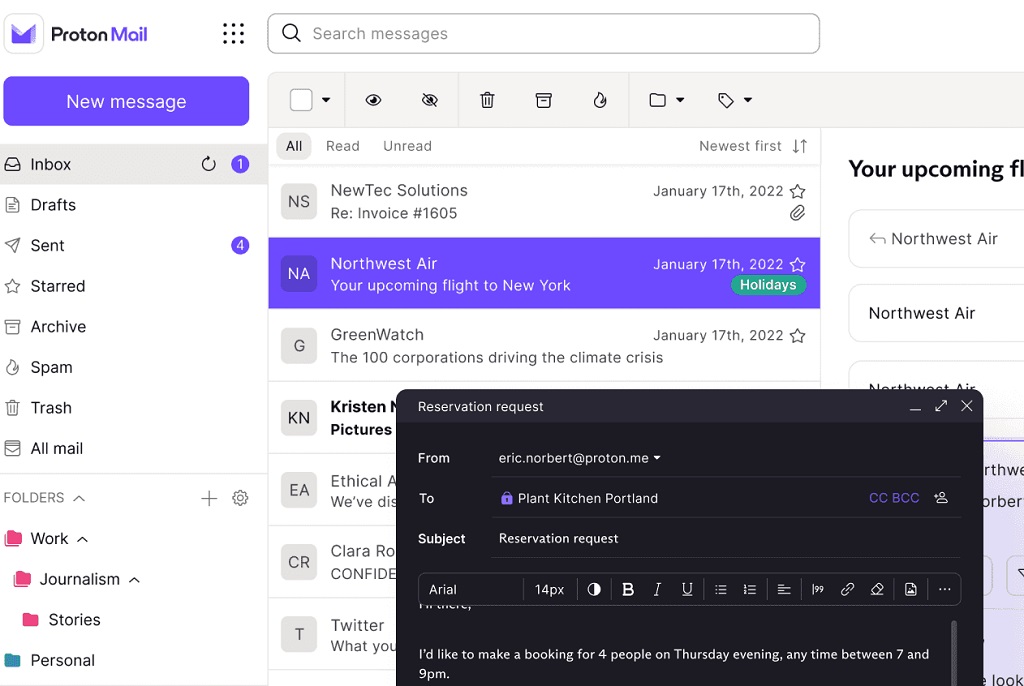
- ProtonMail: This is one of the best anonymous email service providers, and it's free! Your emails are end-to-end encrypted.
- Tutanota: Tutanota encrypts your emails and hides your IP address, so your location can't be discovered even if someone somehow decrypts your mail.
- PrivateMail: PrivateMail offers encrypted email accounts starting from $8.95/month. It encrypts your files using the same 256-bit AES algorithm CyberGhost VPN uses
- Hushmail: Hushmail is a well-established encrypted email service provider that has been catering to businesses for over two decades.
- CounterMail: This anonymous email account provider focuses heavily on security with OpenPGP encryption, SSL server authentication, and two-factor authentication.
Step 2. Creating Your Anonymous Email Account
To create an anonymous email account, visit the website of your chosen service. Follow the instructions to create a new account. Remember, don't provide any personal information that could be traced back to you.
Choose a username that doesn't include your real name or identifiable information. When creating a password, ensure it's strong and unique to protect your account further. Also, consider using a VPN when creating your anonymous email account.
A Virtual Private Network (VPN) can provide an extra layer of security. A VPN hides your IP address, making it harder for your location and identity to be traced. There are many VPN services available, both free and paid.
Choose one that suits your needs and activate it before sending your anonymous email. Remember, while a VPN provides additional security, it's not foolproof. Some services may log your activity, so choose a VPN provider with a strict no-logs policy.
Some of the Best VPNs for anonymity include;
- NordVPN: NordVPN is a highly regarded VPN service known for its robust security features. NordVPN also has a strict no-logs policy, meaning they don't track, collect, or share your private data.
- Surfshark: Surfshark is another VPN service with excellent security and privacy features. Like NordVPN, Surfshark encrypts your internet traffic and hides your IP address, making your email communications more secure.
- ExpressVPN: ExpressVPN is known for its high speed and strong security measures. It uses AES-256, a top-of-the-line encryption standard, to secure internet traffic.
Read: Beginner's Guide to Virtual Private Networks
Step 3. Composing and Sending Your Email
You can compose your email once your account is set up and your VPN is active. Write your message, enter the recipient's email address, and hit send. Be careful not to include any information in the body of the email that could reveal your identity.
Before hitting send, double-check your email content to ensure nothing could give away your identity. This includes not only the body of the email but also any attachments. If you're sending a document, ensure it doesn't contain personal information or metadata that could reveal your identity.
Other Tips when composing and sending your anonymous email include;
- Avoid Including Personal Information: Don't include any personal information in your email that could be traced back to you. This includes your real name, location, workplace, or other identifiable details.
- Be Careful with Your Writing Style: If the recipient knows you, they may recognize your writing style. Try to write in a neutral style that doesn't give away your identity.
- Don't Send to Known Contacts: If you want to remain anonymous, avoid emailing people who know you. They're more likely to recognize clues about your identity.
- Check Your Attachments: If you send attachments, make sure they don't contain any metadata or hidden information that could reveal your identity.
- Don't Log In to Other Accounts: If you're logged in to other services (like Google or Facebook) while sending an anonymous email, those services may track your activity and link it back to your identity.
Step 4. Delete Your Anonymous Email Account
If you want to ensure that your anonymous email cannot be traced back to you, consider deleting your anonymous email account after sending your message. This is especially important if you used a service requiring personal information during sign-up.
Remember, digital footprints can be traced, so it's best to leave as little information behind as possible.
Limitations of Using Anonymous Email Services
While these steps can help protect your identity, it's essential to understand that absolute anonymity is difficult. Skilled hackers or law enforcement agencies may still be able to trace your email back to you.
In fact, anonymous email services have many other limitations and shortcomings;
- Not Always Completely Anonymous: Even with an anonymous email service, absolute anonymity is difficult.
- Limited Features: Anonymous email services often have fewer features than traditional email providers.
- Limited Support: Many anonymous email services are free or low-cost and may offer less customer support than traditional email providers.
- Potential for Abuse: Unfortunately, anonymous email services can be misused for illegal activities, such as sending spam or engaging in cybercrime.
- Data Retention Policies: While many anonymous email services have strict no-logs policies, some may retain specific data for some time.
- Dependence on Trust: Using an anonymous email service requires trusting the provider to maintain your privacy and security.
- Usability: Some anonymous email services may not be as user-friendly or intuitive as mainstream ones. This could make them more challenging to use for some people.
Other Things to Note When Sending Anonymous Email
I've provided a relatively basic process for sending anonymous emails, along with some guidelines. However, there's always room for improvement and other things you can take additional steps to increase your privacy.
For example;
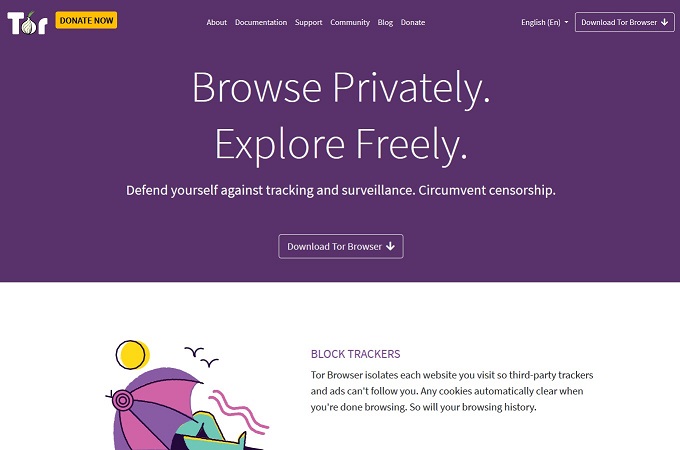
Consider Using Tor
For an added layer of anonymity, consider using Tor, a free service that enables anonymous communication. Tor achieves this by directing internet traffic through a free, worldwide volunteer overlay network.
This can help conceal your location and usage from anyone conducting network surveillance or traffic analysis. However, while Tor can enhance your privacy, it also has limitations and vulnerabilities. To use Tor, you'll need to download the Tor browser, a modified version of Mozilla Firefox.
Be Mindful of Metadata
Even when using an anonymous email service, emails can still contain metadata. This information is data about the email itself, such as the time it was sent. Some services do a better job than others at stripping this metadata from your emails, but it's something to be aware of.
Respect Privacy and Legal Boundaries
While sending an anonymous email can protect your privacy, it's essential to respect the privacy of others. Never use anonymous emails to harass, threaten, or harm others. Also, be aware of the legal implications of your actions.
In many jurisdictions, specific uses of anonymous emails may be illegal. For example, sending unsolicited spam or threats or engaging in unlawful activities using anonymous emails can lead to serious legal repercussions.
Final Thoughts: Anonymity is Not an Excuse to Ignore The Law
In the digital age, where our lives are increasingly online, understanding how to communicate anonymously is a valuable skill. Whether you're a whistleblower, a privacy advocate, or someone who values their privacy, knowing how to send an anonymous email can help you communicate more securely.
Sending an anonymous email involves more than just creating a new email account. It requires a careful understanding of online privacy and security measures. By following these steps, you can maintain your privacy while communicating online.
However, while anonymous email services offer higher privacy and security than mainstream email providers, it's important to remember that no system is foolproof. Absolute anonymity is difficult to achieve, and these tools should be used responsibly.