Robust security measures are paramount as we rely on wireless networks to connect our devices. One such security measure is the Network Security Key – a term that is often heard but seldom fully understood.
We live in an increasingly interconnected world. Digital communication and information exchange has become the norm, and safeguarding our networks has become a critical concern. Understanding how network security keys work can play a role in protecting our digital assets.
What is a Network Security Key?
In its simplest form, a network security key is a password or encryption key that grants authorized access to a wireless network. It serves as a digital key to unlock the virtual doors of your network, allowing only authorized individuals or devices to connect and interact.
By implementing this layer of security, you can prevent unauthorized access, safeguard sensitive information, and preserve the integrity of your digital infrastructure.
Protect Your Online Activities
Always use a VPN when connected to the Internet. It masks your devices and encrypts all your data to ensure a safer browsing experience. Check out our Best VPN Recommendations.
Types of Network Security Keys
Several security key types are used today: WEP, WPA, WPA2, and WPA3. Due to the many types of devices, not all may be compatible with some of these types of keys, hence a broad range of discrepancies.
Wired Equivalent Privacy (WEP)
WEP was one of the earliest encryption protocols used to secure wireless networks. It uses a 40-bit or 104-bit key to encrypt data transmitted over the network. However, WEP is considered weak and vulnerable to attacks, and its usage is not recommended due to its susceptibility to hacking.
WiFi Protected Access (WPA)
WPA is an improved security protocol designed to replace WEP. It offers more robust encryption and security features compared to WEP. WPA utilizes a Pre-Shared Key (PSK) or a passphrase as the network security key.
The key can combine letters, numbers, and symbols, making cracking harder than WEP keys. WPA provides a higher level of security than WEP and is a recommended choice for securing wireless networks.
WPA2
WPA2 is the current standard for securing wireless networks. It enhances the security of WPA by implementing more robust encryption algorithms, such as Advanced Encryption Standard (AES). WPA2 supports both Personal and Enterprise modes.
In Personal mode, a Pre-Shared Key (PSK) is used as the network security key, similar to WPA. A more robust authentication method, such as Extensible Authentication Protocol (EAP), is used in the Enterprise mode.
WPA3
WPA3 is the latest and most advanced wireless security protocol. It addresses some vulnerabilities found in WPA2 and introduces new security features. WPA3 provides enhanced protection against brute-force attacks and improves encryption for open networks.
It also introduces a Simultaneous Authentication of Equals (SAE) algorithm that makes it harder for attackers to guess the network security key. WPA3 is highly recommended for securing Wi-Fi networks, especially for newer devices that support it.
Enterprise Authentication
In addition to the aforementioned network security keys, enterprise networks often employ more advanced authentication methods, such as digital certificates or RADIUS servers. These methods offer higher levels of security, particularly for large organizations that require centralized authentication and access control.
What is the Purpose of a Network Security Key?
A network security key helps ensure a wireless network's security and privacy. It acts as a digital lock, allowing only authorized devices to access and communicate with the network. Here are the essential purposes of a network security key:
Access Control: The primary purpose of a network security key is to control access to the wireless network. Requiring a valid security key prevents unauthorized devices from connecting and accessing network resources.
Authentication: The network security key is a form of authentication for devices attempting to join the network. Only devices with the correct key can connect, verifying their identity as authorized users.
Data Encryption: A network security key encrypts the data transmitted over the wireless network. It ensures that the information exchanged between devices is scrambled and unreadable to anyone without the correct key, providing confidentiality and preventing eavesdropping.
Security Against Intruders: Using a solid network security key protects the wireless network against potential intruders or attackers. It acts as a barrier, making it more difficult for unauthorized individuals to gain access and compromise the network's integrity.
Privacy and Confidentiality: A network security key plays a crucial role in maintaining privacy and confidentiality within the wireless network. It prevents sensitive data from being intercepted or accessed by unauthorized users, ensuring that only authorized individuals or devices can access confidential information.
Protection against Network Attacks: Implementing a network security key helps protect against various network attacks, such as unauthorized access, spoofing, or man-in-the-middle attacks. It adds an extra layer of security to the network infrastructure, reducing the risk of data breaches and unauthorized activities.
How to Create a Strong Network Security Key
Creating a robust network security key is essential for ensuring the security of your wireless network. Robust keys enhance the protection of your wireless network and minimize the risk of unauthorized access or data breaches.
Here are some tips to help you create a robust and secure network security key:
- Make your network security key long and complex. Aim for at least 12 characters, including a combination of uppercase and lowercase letters, numbers, and special symbols.
- Avoid using common words, dictionary words, or guessable information like your name, address, or birthdate.
- Generate your network security key randomly rather than using easily predictable patterns.
- Do not include personal information in your network security key, such as your name, phone number, or social security number.
- Consider changing your network security key periodically to add an extra layer of security.
Where to Find Your Network Security Key
How to Fix The Network Security Key Mismatch Error
Network security key mismatches can occur when a client and server computer cannot agree on the network security key. If you encounter a Network Security Key Mismatch error while trying to connect to a wireless network, here are some troubleshooting steps to resolve the issue:
Double-check the Key
Make sure you have entered the network security key correctly. It's essential to input the key accurately, including uppercase and lowercase letters, numbers, and special characters. Even a minor typing mistake can result in a mismatch error.
Verify the Network Security Key
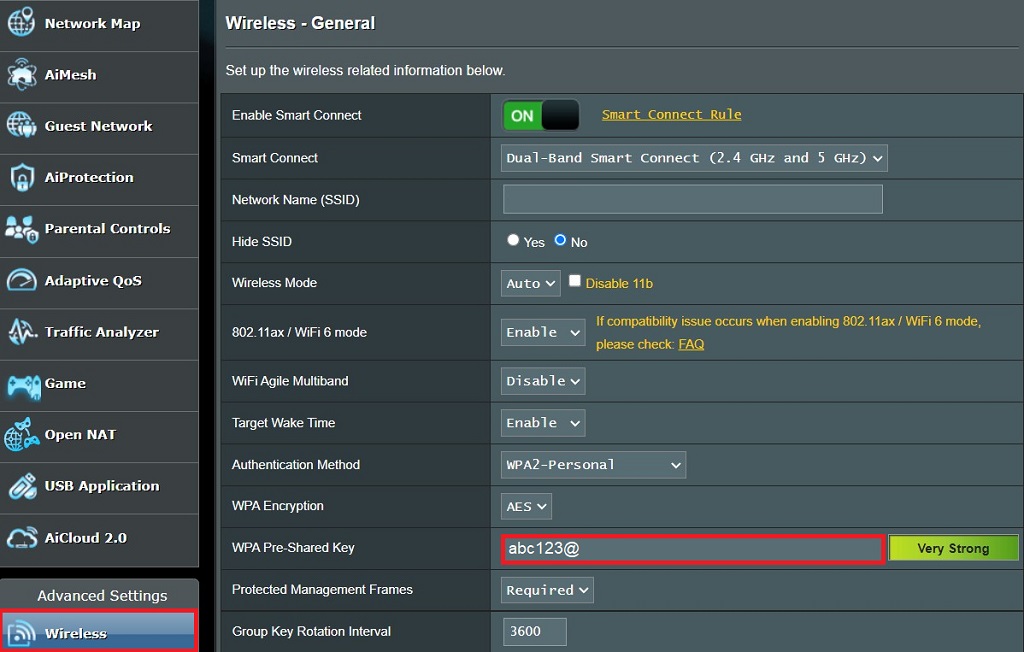
Confirm that your network security key matches the one configured on the wireless router or access point. Check the router's label, administration interface, or documentation to ensure you have the correct key.
Restart Your Devices
Sometimes, connectivity issues can be resolved by restarting the devices involved. Restart your computer, smartphone, tablet, and router or access point. After restarting, try connecting again and entering the network security key.
Update Your Wireless Drivers
Outdated or incompatible wireless drivers can cause connectivity issues. Update the drivers for your wireless network adapter by visiting the manufacturer's website or using the device manager on your computer.
Reset Your Network Settings
Resetting network settings can help resolve configuration conflicts. On your computer or mobile device, navigate to the network settings menu and choose to reset network settings. After the reset, reconnect to the network and enter the security key.
Check The Settings on Your Router
Access the router's administration interface through a web browser. Ensure that the network security key settings on the router match the one you are entering. If necessary, reconfigure the security settings on the router and update the network security key.
Disable Security Software
Temporarily disable any third-party security software on your computer, such as antivirus or firewall programs. These programs can sometimes interfere with network connections. After disabling them, try connecting again to see if the mismatch error persists.
Perform a Router Factory Reset
As a last resort, you can reset the router to factory settings. Remember that this will erase all customized settings, so make sure to have a backup of your configuration. Refer to the router's documentation for instructions on how to perform a reset.
Enhance Your Network Security With a VPN
Protect Your Privacy With NordVPN
Take control of your digital life and enjoy safe browsing and private communications. Get NordVPN today and experience the best in digital privacy and security.
While a network security key is crucial for securing your wireless network, you can further enhance your network security by incorporating a Virtual Private Network (VPN). Combining a network security key with a VPN can create a robust defense system for your network.
Here's how a VPN can strengthen your network security:
Additional Layer of Encryption
While a network security key encrypts the data transmitted between devices on your wireless network, a VPN adds an extra layer of encryption. When you connect to a VPN, all your internet traffic is encrypted from your device to the VPN server.
This double layer of encryption makes it extremely challenging for anyone to intercept and decipher your data, ensuring your network traffic remains secure.
Secure Remote Access
A VPN enables secure remote access to your network resources. This benefits business with employees working remotely or accessing sensitive company resources. Combining a network security key and a VPN ensures that remote access is encrypted and protected from unauthorized access.
Anonymity and Privacy
While a network security key ensures authorized access to your wireless network, a VPN provides an additional layer of privacy and anonymity. By masking your IP address and routing your internet traffic through VPN servers, a VPN prevents third parties, including your ISP or government agencies, from monitoring your online activities.
Bypassing Network Restrictions
In addition to securing your network, a VPN allows you to bypass network restrictions and access geo-restricted content or websites. By connecting to VPN servers in different locations, you can overcome regional limitations and access online resources that may be blocked or unavailable.
Network Security Keys Are Important Even in Home Environments
While most modern-day threats involve malware or ransomware, you must be aware of a much more dangerous cyber threat: hackers. While most hacks today serve to extract sensitive information from your computer, the future may hold far more damaging consequences.
Always ensure that you are using a network security key and that it is at the forefront of your security awareness checklist to help keep data from falling into the wrong hands.