Today, Virtual Private Networks (VPNs) are often touted as pillars of anonymity and security. However, it's essential to understand that nothing in life is perfect. Despite their many advantages, several VPN security risks still exist.
It isn't impossible to work around these security loopholes. As long as you know what they are, safeguarding against VPN security risks is possible. Knowledge is power, as they say, so let's learn how to better protect ourselves online – even with a VPN.
Here are 8 VPN security risks you need to safeguard against:
1. The Illusion of Complete Anonymity
A standard narrative by VPN proponents suggests that your online presence is entirely anonymous with a VPN. However, this is a partial truth that needs a closer look. After all, not all VPNs are created equal.
Some VPNs may log user activities, some may have weak security, and others might comply with government requests. For example, Fox News revealed that in 2023, SuperVPN suffered a security breach that exposed data of over 360 million users.
Worse still is that the incident is not unique. Several other VPN brands have left their customers high and dry over the years.
Mitigating the Risk
- Research VPN providers' data logging policies.
- Choose VPNs based in privacy-friendly jurisdictions.
- Use Tor with VPN for extra anonymity.
- Read independent VPN reviews and privacy policies.
- Understand the legal compliance of VPN providers.
2. Risk of Malware and Adware
Free or inexpensively priced VPN services sometimes come with the risk of malware and adware. These nefarious software pieces can be stealthily bundled with VPN software. As such, the allure of ‘free' often comes at a significant, albeit hidden, cost.
Malware, once installed, can wreak havoc on your device, compromising your personal information and digital security. Adware, while less malicious, can inundate your browsing experience with unwanted ads.
Some VPN brands have also been explicitly targeted by malware. For instance, Malwarebytes Labs indicated that CISCO VPNs operating without multifactor authentication were under attack by Akira ransomware.
Mitigating the Risk
- Avoid free or low-cost VPN services.
- Opt for reputable, paid VPN providers.
- Read user reviews and expert testimonials.
- Install and update reliable antivirus software.
- Check VPN app permissions during installation.
3. Encryption Quality Issues
Not all VPNs are equal in their encryption strength. Some use robust, state-of-the-art encryption standards, while others may cut corners with outdated or weaker protocols. The latter will leave your data vulnerable to interception and decryption.
This variance in encryption quality is a significant concern. Weaker encryption can be more easily cracked by sophisticated hackers, exposing your sensitive information. This risk becomes significantly pronounced when using VPNs for sensitive activities.
Mitigating the Risk
- Choose VPNs with AES-256 encryption.
- Avoid outdated protocols like PPTP.
- Regularly update VPN software.
- Verify encryption standards with the provider.
- Stay informed on encryption advancements.
4. IP and DNS Leaks
IP and DNS leaks occur when your actual IP address or the websites you visit are exposed due to flaws in the VPN software. This can happen even when you believe you are safely connected to a VPN, thus undermining the very purpose of using one.
IP leaks reveal your location and internet service provider, while DNS leaks expose your browsing history. Both types of leaks can severely compromise your online anonymity and privacy.
The Daily Dot noted a list of 17 VPNs that were found to leak such data. Included in the list were HolaVPN, Touch VPN, and AzireVPN.
Mitigating the Risk
- Use VPNs with leak protection features.
- Regularly test VPN for IP/DNS leaks.
- Employ VPNs with automatic kill switches.
- Choose VPNs with private DNS servers.
- Perform leak tests after software updates.
5. Session Logging and Tracking
Despite the primary use of VPNs being privacy and anonymity, some VPN providers keep logs of user activities. This data can include information about your browsing habits, connection times, and even IP addresses.
In the event of a data breach or a legal request, these logs can be exposed, compromising your privacy. The risk is particularly pronounced with free or low-cost VPN services. These providers might track and sell your data to third parties.
Mitigating the Risk
- Select VPNs with a strict no-logs policy.
- Verify the provider's logging policy independently.
- Prefer VPNs audited by third-party security firms.
- Be cautious with free VPN services.
- Regularly review and understand VPN privacy policies.
6. Blocking by Websites and Services
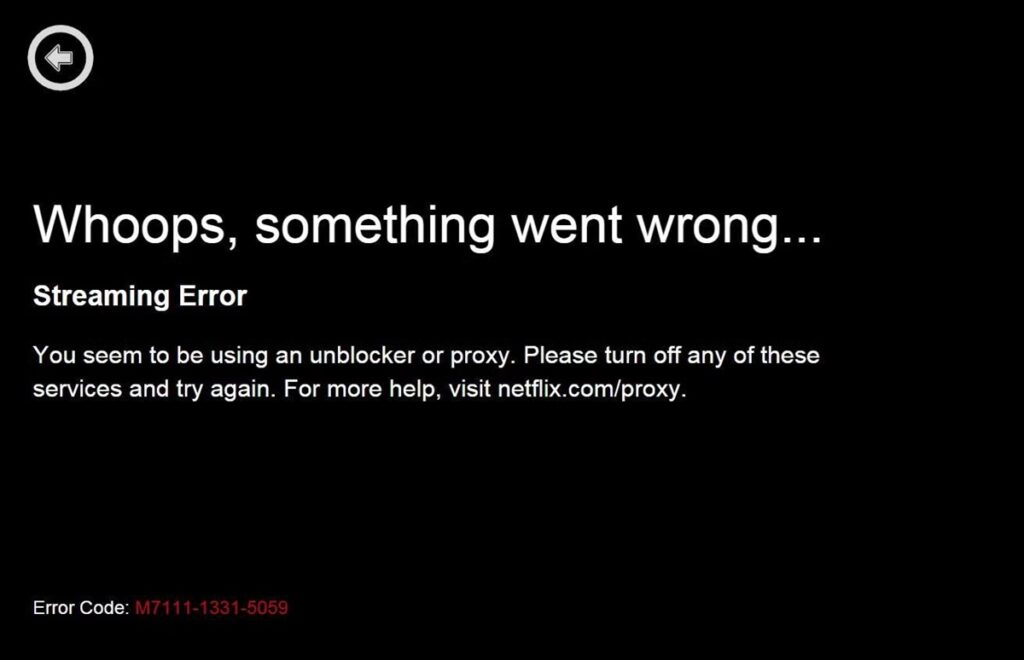
An increasingly common challenge for VPN users is websites becoming more capable of blocking anonymizer services. This is particularly true for streaming services, financial institutions, and even some government websites.
Netflix, for example, has seriously ramped up its anti-VPN measures. They employ sophisticated technology to detect and block VPN users. The aim of this is to enforce geo-restrictions or prevent fraudulent activities.
Mitigating the Risk
- Use VPNs that offer stealth or obfuscation technology.
- Switch between different servers or IP addresses.
- Opt for VPNs that regularly update their server IPs.
- Avoid using VPNs for websites that explicitly prohibit them.
- Consider dedicated or residential IP VPN services.
7. Shadow IT in Corporate Networks
Shadow IT refers to using unauthorized software or systems, like VPNs, within a corporate environment. Employees may use these services for various reasons, such as bypassing network restrictions or enhancing personal privacy.
However, this unauthorized use can pose significant security risks to the organization. It can lead to data breaches, non-compliance with regulatory standards, and network vulnerabilities. Shadow IT operates outside the purview of most IT departments.
Mitigating the Risk
- Establish clear IT policies and communicate them.
- Provide approved VPN solutions for employees.
- Conduct regular IT audits and network monitoring.
- Educate employees about the risks of unauthorized VPNs.
- Implement strong network security measures.
8. Software Vulnerabilities
Like any other software, VPN software can have vulnerabilities that hackers might exploit. These vulnerabilities can range from minor bugs to severe security flaws compromising user data and privacy.
Keeping the software updated is crucial. However, even updated software can have undisclosed vulnerabilities. Knowing the possibility is there should be a critical factor in ensuring you don't put your entire faith in a VPN.
Mitigating the Risk
- Regularly update your VPN software.
- Choose VPNs with a strong track record of security.
- Monitor VPN security bulletins and updates.
- Use additional security tools like firewalls and antivirus.
- Stay informed about common VPN vulnerabilities.
Examples of VPN Security Risk Incidents
Over the years, several notable incidents have been involving VPN vulnerabilities, each providing valuable lessons in digital security. However, remember that these aren't the only occurrences; just the tip of the iceberg:
- 21 million data records, including credentials and device data, were stolen from SuperVPN, GeckoVPN, and ChatVPN. The data was being sold on a hacker forum in 2023.
- A vulnerability in Fortinet VPN was exploited by Chinese hackers in 2022. The attackers used the Boldmove backdoor in a zero-day attempted heist.
- Attackers attempted to hack US government agencies thrice in 2021 via their Pulse Connect Secure VPN. The attempts were aimed at the government's supply chain capabilities.
Final Thoughts
While VPNs offer a shield of privacy and a layer of security, it is undeniable that VPN security risks are part and parcel of the deal. VPNs are not infallible. Nothing in the world of IT is impenetrable or unhackable.
The key takeaway here is not to dissuade you from using VPNs. Instead, we want to highlight that the web is a dangerous place. Awareness of VPN security risks will allow you to safeguard your digital privacy and security better.